Introduction
Zero trust security is a modern approach to cybersecurity that focuses on strict identity verification for every user and device. Unlike traditional security models, zero trust security assumes that threats can exist both inside and outside a network.
As cyber threats continue to grow, zero trust security is becoming an essential strategy for protecting sensitive data and systems.
What Is Zero Trust Security?
Zero trust security is a framework that requires all users and devices to be verified before accessing any system or data. It follows the principle of “never trust, always verify.”
Instead of trusting users inside a network, zero trust model continuously checks identity and access permissions.
How Zero Trust Security Works
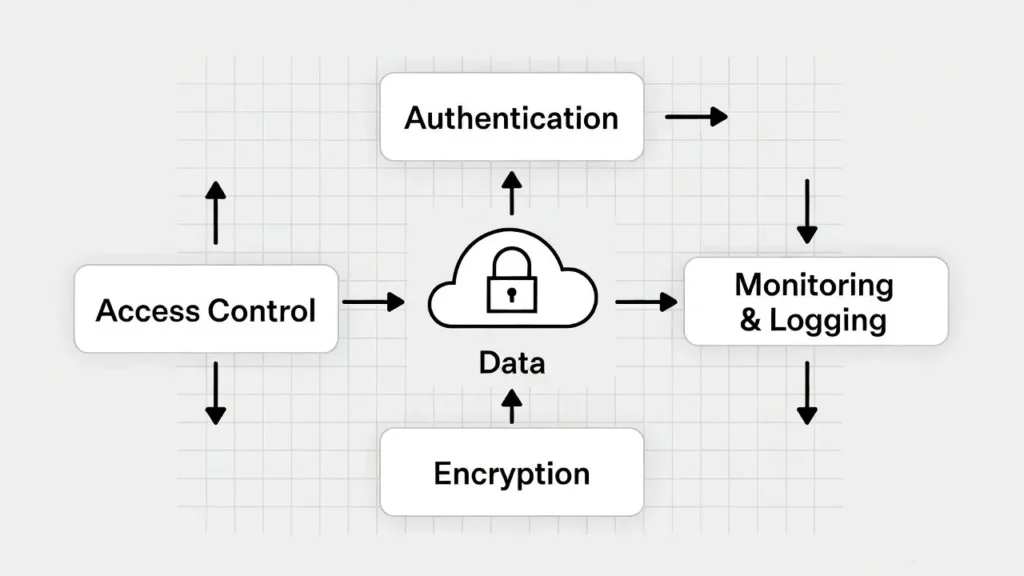
To understand zero trust model, it is important to look at its key components.
Identity Verification
Every user must prove their identity using authentication methods.
Device Security
Devices are checked to ensure they meet security standards.
Access Control
Users are given only the access they need.
Continuous Monitoring
Systems monitor activity to detect suspicious behavior.
This approach ensures that zero trust security reduces the risk of unauthorized access.
5 Powerful Benefits of Zero Trust Security
1. Stronger Data Protection
The zero trust model protects sensitive data by limiting access.
2. Reduced Cyber Threats
It minimizes the chances of attacks from both internal and external sources.
3. Better Access Control
Users only get access to what they need.
4. Improved Visibility
Organizations can monitor all activities within the network.
5. Enhanced Security for Remote Work
This approach supports secure access for remote employees.
Applications of Zero Trust Security
This approach is widely used in modern systems.
Cloud Security
It protects cloud-based systems and services.
Business Networks
Companies use zero trust security to secure internal systems.
Remote Work Environments

It ensures safe access for remote users.
Challenges of Zero Trust Security
Despite its advantages, zero trust model has some challenges.
Implementation Complexity
Setting up zero trust model requires planning and resources.
Cost
Initial implementation can be expensive.
User Experience
Frequent verification may affect user convenience.
The Future of Zero Trust Security
The future of zero trust model is closely connected with advancements in cloud computing, artificial intelligence, and automation. As organizations continue to move their data and services to the cloud, the need for stronger and more flexible security systems is increasing. Zero trust model is becoming a preferred approach because it focuses on verifying every user, device, and access request in real time.
Modern technologies such as AI-driven threat detection and behavioral analytics are expected to make zero trust model more intelligent and proactive. These systems can identify unusual patterns and respond to potential threats before they cause damage. In addition, the rise of remote work and hybrid environments has made it essential for businesses to secure access from multiple locations, further increasing the importance of zero trust model.
As cybersecurity challenges continue to evolve, zero trust model will become easier to implement through automated tools and integrated platforms. Organizations of all sizes are expected to adopt this model to protect sensitive data, ensure compliance, and maintain trust in digital systems.
Conclusion
Zero trust security is a powerful and modern approach that improves cybersecurity by verifying every user and device before granting access. By following the principle of “never trust, always verify,” it reduces the risk of data breaches and unauthorized access. This makes zero trust security an essential strategy for protecting both personal and organizational data.
In today’s digital world, where cyber threats are becoming more advanced, relying on traditional security methods is no longer enough. Zero trust security provides a more reliable and scalable solution that adapts to changing environments, including cloud systems and remote work setups. It helps organizations maintain better control over their networks while ensuring secure communication and data protection.
As technology continues to grow, zero trust security will play a key role in shaping the future of cybersecurity. Adopting this approach early can help businesses and individuals stay ahead of potential threats and build a safer digital experience.

