Introduction
As digital technology becomes a part of everyday life, cybersecurity has become more important than ever. From online banking and social media to remote work and cloud storage, our personal and professional data is constantly exposed to potential cyber threats.
Understanding common cybersecurity risks can help individuals and businesses protect their information and stay safe online.
In this guide, we’ll explore the most common cybersecurity threats and practical steps to reduce risk.
What Are Cybersecurity Threats?
Cybersecurity threats are malicious attempts to access, damage, or steal data from digital systems, networks, or devices. These threats can target individuals, organizations, and even governments.
They often exploit human behavior, software vulnerabilities, or weak security practices.
1. Phishing Attacks
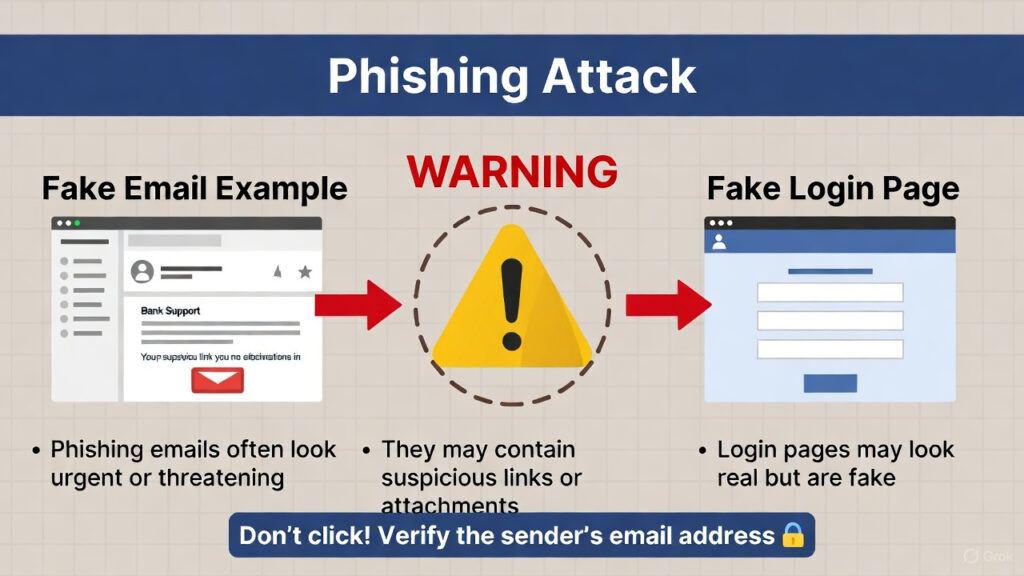
Phishing is one of the most common cyber threats, where attackers trick users into revealing sensitive information such as passwords or financial details.
Examples
- Fake emails pretending to be banks
- Fraudulent login pages
- Scam messages with malicious links
Prevention Tips
- Verify sender identity
- Avoid clicking suspicious links
- Enable two-factor authentication
2. Malware

Malware refers to malicious software designed to damage or disrupt systems.
Types of Malware
- Viruses
- Worms
- Spyware
- Trojans
Malware can spread through downloads, email attachments, and compromised websites.
3. Ransomware
Ransomware locks users out of their data or systems until a ransom is paid.
Impact
- Data loss
- Financial damage
- Operational disruption
Regular backups and software updates can reduce risk.
4. Password Attacks
- Brute-force attacks
- Credential stuffing
- Dictionary attacks
Using strong and unique passwords significantly improves security.
5. Social Engineering
Social engineering manipulates human behavior to gain unauthorized access.
Examples
- Impersonation scams
- Fake tech support calls
- Insider manipulation
Awareness and verification are key defenses.
6. Identity Theft
Identity theft occurs when attackers steal personal information to commit fraud.
Risks
- Financial fraud
- Account takeover
- Privacy violations
Monitoring accounts and securing personal data helps prevent identity theft.
7. Distributed Denial-of-Service (DDoS) Attacks
DDoS attacks overwhelm systems or websites with excessive traffic, making them unavailable.
These attacks often target businesses and online services.
8. Man-in-the-Middle (MitM) Attacks
In MitM attacks, attackers intercept communication between two parties.
Common Scenarios
- Public Wi-Fi interception
- Fake network hotspots
Using secure networks and encryption reduces risk.
How to Stay Safe Online
🔐 Use Strong Passwords
Create complex passwords and avoid reuse.
📲 Enable Two-Factor Authentication
Adds an extra layer of security.
🔄 Keep Software Updated
Updates fix vulnerabilities.
📡 Avoid Public Wi-Fi Risks
Use VPNs or secure networks when possible.
📁 Backup Important Data
Regular backups protect against ransomware.
The Future of Cybersecurity
As technology evolves, cybersecurity will increasingly rely on:
- AI-powered threat detection
- Behavioral analytics
- Zero-trust security models
- Advanced encryption technologies
Cybersecurity awareness will remain essential for both individuals and organizations.
Conclusion
Cybersecurity threats continue to evolve alongside digital innovation, making awareness and preventive measures more important than ever. By understanding common cyber risks and adopting safe online practices, individuals can significantly reduce their exposure to attacks.
Cybersecurity is not just a technical issue—it’s a shared responsibility in the digital age.

